Home / Technology / New VPN Protocol Fails Basic Web Access
New VPN Protocol Fails Basic Web Access
15 Apr
Summary
- New VPN protocol only accessed small, unencrypted HTTP URLs.
- Connection failed for secure HTTPS sites due to large packet sizes.
- Users may need to manually fix the protocol's MTU settings.
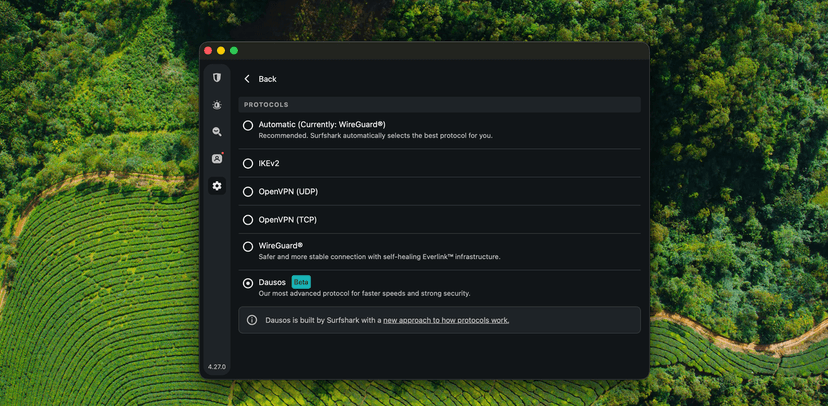
Surfshark launched its proprietary post-quantum VPN protocol, Dausos, on Monday. However, initial testing revealed significant issues, rendering the secure web inaccessible on standard home connections. The protocol appeared to exclusively work when accessing small, unencrypted HTTP URLs and required active connections.
Testing demonstrated that the VPN protocol could not handle the larger data packets necessary for secure HTTPS handshakes. Attempts to access secure websites resulted in connection timeouts, while older, unencrypted HTTP pages loaded successfully. This limitation meant the "next-gen" security protocol surprisingly only functioned with "Not Secure" marked sites.
Further investigation by a colleague on an enterprise network showed mixed results, with the secure web being accessible but underlying connection struggles persisting. This suggests the protocol's "adaptive" qualities might have a blind spot regarding network conditions, particularly with residential PPPoE limits.
Analysis indicated a static MTU setting of 1424 bytes, which is too close to the typical 1492-byte limit for many home routers, especially with the added bulk of post-quantum encryption. The identified solution involved manually overriding the protocol's configuration to force a lower MTU of 1280 bytes, successfully restoring normal web access.
Surfshark has acknowledged the issue, confirming the protocol's configuration clashes with residential PPPoE limits. The company is reportedly issuing an emergency hotfix for approval.